[ad_1]
Two new vulnerabilities impact ConnectWise ScreenConnect, remote desktop and access software used for support: CVE-2024-1709 and CVE-2024-1708, with the former being particularly dangerous for organizations.
The CVE-2024-1709 vulnerability, which affects ScreenConnect 23.9.7 and prior, allows any remote attacker to bypass authentication to delete the ScreenConnect user database and get control of an admin user. Massive exploitation by attackers is ongoing in the wild, with more than 3,000 vulnerable instances reachable from the internet. Security companies have observed ransomware, information stealers and Cobalt Strike payloads, to name a few, being installed after successful exploitation of the vulnerability.
The CVE-2024-1708 vulnerability, which is not as severe as CVE-2024-1709, allows path traversal, which enables an attacker to access files and directories that should not be accessible.
Technical details about the ScreenConnect CVE-2024-1709 vulnerability
U.S.-based cybersecurity company Huntress released technical details about the ScreenConnect CVE-2024-1708 and CVE-2024-1709 vulnerabilities, the latter being particularly dangerous because a simple request to a special path on exposed instances allows an attacker to connect to the setup wizard of the instance (Figure A).
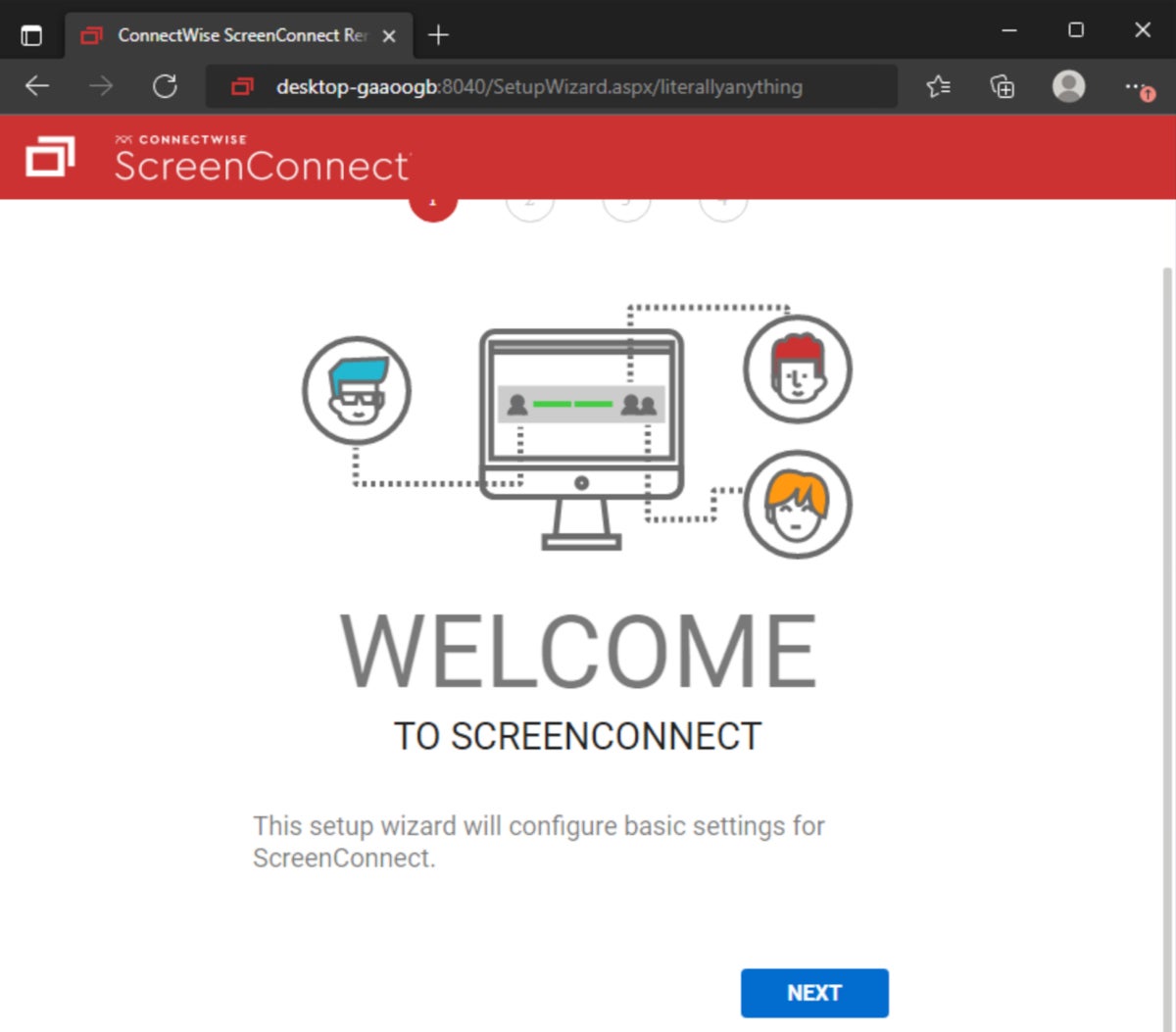
As explained by Huntress researchers, the setup wizard is responsible for setting up the initial admin user and installing a license on the system. The Huntress team wrote, “The user creation portion of this setup happens immediately after clicking the ‘Next’ button on the setup page, so there is no need to complete the setup wizard fully to exploit the system.” If an attacker completes this step, the internal user database will be fully overwritten, and all local users will be deleted, leaving only the attacker as administrator of the instance.
Once this is done, it is trivial to create and upload a malicious ScreenConnect extension to gain full remote code execution on the instance, according to the researchers.
Another vulnerability has also been reported, CVE-2024-1708, which is a less-severe vulnerability allowing path traversal.
Massive exploitation of CVE-2024-1709 in the wild has started
Proof of concept for exploiting CVE-2024-1709 has been published on GitHub, showing how to add a new user to the compromised system.
Cybersecurity company Sophos observed several attacks on Feb. 21, 2024, with attackers dropping ransomware built with the LockBit builder tool on 30 customer networks. Important note: The use of the LockBit ransomware builder tool does not mean that it has ties with the LockBit developers, especially when the LockBit infrastructure was recently taken down. Any cybercriminal with access to the builder can be behind those attacks, and the ransom note observed by Sophos mentioned the “buthtiRansom” variant. Sophos stated that another ransomware based on the LockBit builder called “LockBit Black” was observed but failed to deploy in a customer environment.
Password stealers, RATs and Cobalt Strike payloads
Cybersecurity attacks other than ransomware are currently hitting the exposed vulnerable instances of ScreenConnect; for instance, password stealers (such as Vidar/Redline) or RATs (such as AsyncRAT) have also been observed in the wild after exploitation of the CVE-2024-1709 vulnerability.
Cobalt Strike payloads have also hit exposed ScreenConnect instances. Sophos saw three similar attacks dropping a .cmd file in the temporary folder where ScreenConnect downloads files before executing it. The cmd tried to launch PowerShell to download an additional payload but failed due to endpoint protection.
Thousands of exposed ScreenConnect instances, mostly on U.S.-based IP addresses
ONYPHE, a French cyber defense search engine dedicated to attack surface discovery & attack surface management, provided TechRepublic with statistics about exposed ScreenConnect instances.
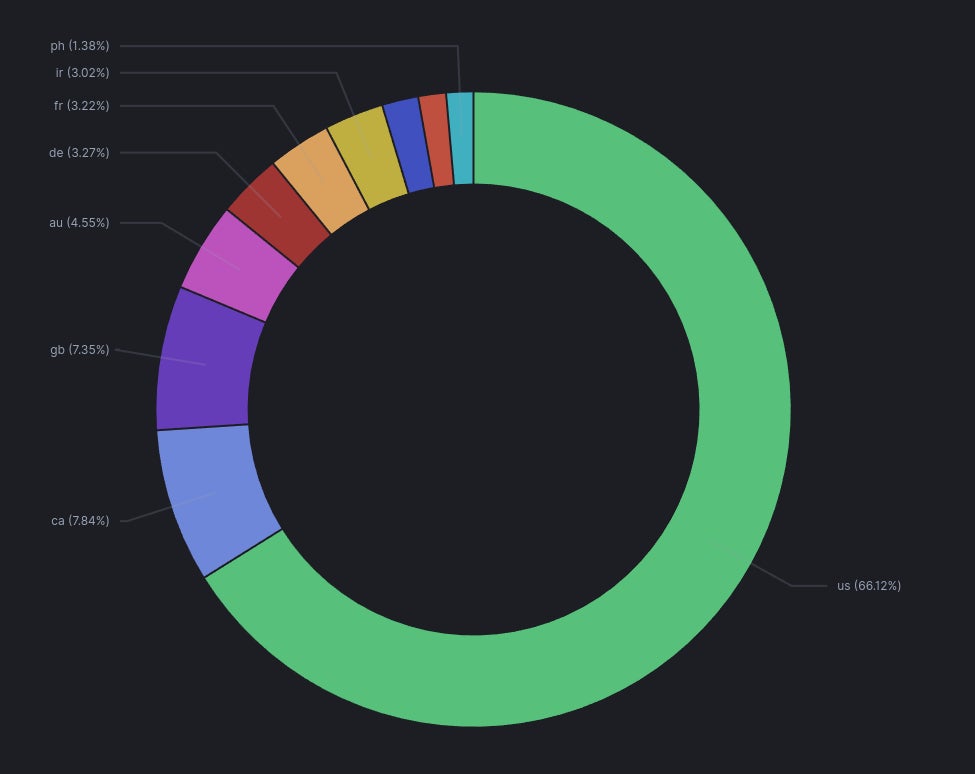
Between Feb. 19-25, 2024, ONYPHE saw 5,731 exposed ScreenConnect unique IP addresses, with 3,284 of those being vulnerable to CVE-2024-1709. Most of those instances are running on U.S.-based IP addresses (66.12%), followed by Canada (7.84%) and the U.K. (7.35%) (Figure B).
How to protect from exploitation via these ConnectWise ScreenConnect vulnerabilities
How to detect exploitation of these ConnectWise ScreenConnect vulnerabilities
Regarding detection, hunting for the pattern “/SetupWizard.aspx/” in server logs might indicate an attack attempt. The “%ProgramFiles(x86)%\ScreenConnect\App_Extensions” folder should also be monitored, as it might be used for storing and executing attackers’ payloads.
SEE: Download this Incident Reporting and Response Procedures Policy from TechRepublic Premium
How to protect your business from these ConnectWise ScreenConnect exploits
ConnectWise indicated in its security bulletin on Feb. 23, 2024 that “they have taken an exception step to support partners no longer under maintenance by making them eligible to install version 22.4 at no additional cost, which will fix CVE-2024-1709.”
ConnectWise recommends on-premise partners immediately update ScreenConnect to 23.9.8 or higher to remediate reported vulnerabilities. ConnectWise has also rolled out an additional mitigation step for unpatched, on-premise users that suspends an instance if it is not on version 23.9.8 or later.
Cloud partners are remediated against the vulnerabilities reported by ConnectWise. On-prem partners are advised to immediately upgrade to the latest version of ScreenConnect. ConnectWise has removed license restrictions, so partners no longer under maintenance can upgrade to the latest version of ScreenConnect.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.
[ad_2]